IKYK002I PKCS#11 token unavailable for icsfpkcs11::genKeyPair with return code 0xe0. The request is not processed.
IKYC010I Error 791740499 returned from CP_NewKeysCreate: Unable to generate or store a public/private key pair through ICSF
IKYC010I Error 791740499 returned from JNH_create_certificate: Unable to generate or store a public/private key pair through ICSF
In pkiserve.conf is TokenName=PKISRVD.PKITOKEN.
The PKIServer does not have UPDATE access to SO.PKISRVD.PKITOKEN and update access to USER.PKISRVD.PKITOKEN .
Note: Defining a token using the ICSF ISPF panels, you can only enter the value in upper case. The PKI documentation describes it in lower case.
IKYP050I PKI SERVICES COULD NOT START BECAUSE ICSF IS UNAVAILABLE
Check for other messages, for example
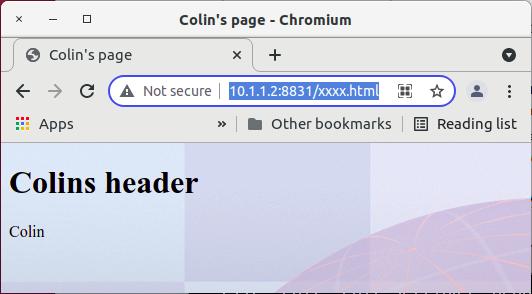
ICH408I USER(PKISRVD ) GROUP(SYS1 ) NAME(COLINS )
CSF1TRL CL(CSFSERV )
INSUFFICIENT ACCESS AUTHORITY
ACCESS INTENT(READ ) ACCESS ALLOWED(NONE )
AH00526: … \xac
I got AH00526:
Syntax error on line … of…: RewriteRule: bad argument line ‘\xac/…
This was because I had ^ and I needed ¬ in the documents.
The USS command chtag -p /u/mqweb3/conf/443.conf gave me
untagged T=off /u/mqweb3/conf/443.conf
My 3270 emulator code page was Bracket CP 037 modified.
Using the ISPF edit command hex on, showed the correct hex data is x’5f’. This can display as ¬ or as ^ depending on your 3270 emulator.
IKYC901I Error 76677164 initializing ICL: The CA certificate in the ICL does not match the one in the keyring
I got this when I redefined my userids and keyrings. I recreated the VSAM files. Display the ICL VSAM file
export PATH=/usr/lpp/pkiserv/bin/
export LIBPATH=/usr/lpp/pkiserv/lib
export NLSPATH=/usr/lpp/pkiserv/lib//usr/lpp/nls/msg/%L/%N
/usr/lpp/pkiserv/bin/iclview -d \’PKISRVD.VSAM.ICL\’
Need to escape the data set name.
My file was empty, so I recreated the VSAM data sets.
IKYP022I Unable to register PKI Services for restart: Error 12, Reason 0x160
This server has not been set up for ARM (Automatic Restart Management). The return code makes no sense to me.
Ignore it.
IKYC009I LDAP post unsuccessful for object id = 101, state = 0x2150000, status =
581500960: No such object
IKYP039E DIRECTORY POST UNSUCCESSFUL. ERROR CODE = 581500960
Unable to get the CA DN from the LDAP server. Check the suffix (eg CN=PKICA,OU=SSS,O=ZZUR COMPANY
IKYP040I PKI SERVICES DOES NOT HAVE KEY GENERATION CAPABILITY
You are missing the TokenName such as
[SAF]
KeyRing=PKISRVD/CARING
TokenName=PKISRVD.PKIToken
in /etc/pkiserv/pkiserv.conf.
This in turn caused rc 0 safrc 8 racfrc 8 racfrs 64 with function GENCERT in IRRSPX00 (R_pkiserve).
In the PKISERVD log (with debug trace turned on)
POLICY IKYK001I Unexpected PKCS#11 icsfpkcs11::genKeyPair return code 0x190. The request is not processed.
CORE IKYC010I Error 791740499 returned from CP_NewKeysCreate: Unable to generate or store a public/private key pair through ICSF
CORE IKYC010I Error 791740499 returned from JNH_create_certificate: Unable to generate or store a public/private key pair through ICSF
httpd: SSL0278E: SSL Handshake Failed, ICSF error. Review ‘RACF
CSFSERV Resource Requirements’ of the z/OS infocenter for
webserver userid requirements. [10.1.0.2:59342 ->
10.1.1.2:443]
This took me two days to find this. The HTTP doc said
SSL0278E: SSL Handshake Failed, ICSF error. Review ‘RACF CSFSERV Resource Requirements’ of the z/OS documentation.
Reason: The webservers userid does not have access to CSFSERV resource classes required for SSL.
Solution: Configure the ICSF started task and allow access to the CSFSRV resources, or disable ECDHE and AES-GCM based ciphers.
The following certificate in the keyring worked
- Signing Algorithm: sha256RSA
- Key Usage: HANDSHAKE
- Key Type: NIST ECC
- Key Size: 521
The following did not work
- Signing Algorithm: sha256RSA
- Key Usage: HANDSHAKE, KEYAGREE
- Key Type: NIST ECC
- Key Size: 256
The only difference seems to be the key size.
httpd: SSL0222W: SSL Handshake Failed, No ciphers specified (no shared
ciphers or no shared protocols).
During a TLS handshake there was no matching certificate found for the client.
I added
SSLCipherSpec TLS_AES_128_GCM_SHA256
SSLCipherSpec TLS_AES_256_GCM_SHA384
SSLCipherSpec TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
SSLCipherSpec TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
SSLCipherSpec TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
SSLCipherSpec TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
SSLCipherSpec TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
SSLCipherSpec TLS_RSA_WITH_AES_128_GCM_SHA256
SSLCipherSpec TLS_RSA_WITH_AES_256_GCM_SHA384
SSLCipherSpec TLS_RSA_WITH_AES_128_CBC_SHA
SSLCipherSpec TLS_RSA_WITH_AES_256_CBC_SHA
SSLCipherSpec TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
ICH408I USER(…) GROUP(…) NAME(…)
NOT AUTHORIZED TO REQUEST DIGITAL CERTIFICATES
I got
ICH408I NOT AUTHORIZED TO GENERATE DIGITAL CERTIFICATES
when the userid did not have >=read access to the appropriate IRR.DIGTCERT.* profile,
PERMIT IRR.DIGTCERT.GENCERT CLASS(FACILITY) ID(ADCDA ) ACCESS(read )
setropts raclist(FACILITY) refresh
ICH408I USER(…) GROUP(…) NAME(ADCDA )NOT AUTHORIZED TO ADMINISTER DIGITAL CERTIFICATES OR CERTIFICATE REQUESTS. READ DENIED
and
IKYI002I SAF Service IRRSPX00 Returned SAF RC = 8 RACF RC = 8 RACF RSN = 8 Request denied, not authorized.
The user issuing the request was not authorised to IRR.RPKISERV.PKIADMIN CLASS(FACILITY).
Note what the message says
- READ DENIED
- UPDATE DENIED
Use
tso rlist facility irr.RPKISERV.PKIADmin auth
and connect the userid ( if required) to a group or give the required access with
PERMIT IRR.RPKISERV.PKIADMIN CLASS(FACILITY)
ID(ADCDA ) ACCESS(read )setropts raclist(FACILITY) refresh
(163) EDC5163I SAF/RACF
extract error. (errno2 = 0x0BE8081C ): …
pthread_security_applid_np(__CREATE_SECURITY_ENV,
__CERTIFICATE_IDENTITY, 32, …, NULL, 0,… returned -1,
errno 163 errno2 be8081c 0x0be8081
The userid being used is revoked
EDC5130I Exec format error. (errno2=0x0B1B0C27)
I got this trying to run a rexx exec within Apache HTTPD. The rexx did not have /* REXX */ as the first line.
IEW2646W 5383 ESD RMODE(24) CONFLICTS WITH USER-SPECIFIED RMODE(ANY) FOR SECTION …. CLASS B_TEXT.
IEW2646W 5383 ESD RMODE(24) CONFLICTS WITH USER-SPECIFIED RMODE(ANY) FOR SECTION … CLASS B_LIT.
I got these trying to bind a C program. I also had an assembler stub which caused this problem.
I added the RMODE and AMODE to my assembler program and cured the problem
CALLPRTF RMODE ANY
CALLPRTF AMODE ANY
CALLPRTF CSECT
IRRSPX00 R_PKIServ rc 0 safrc 8 racfrc 8 racfrs 72
With MODIFYCERTS (delete) I got
One or more certificates cannot be set up for automatic renewal.
SerialNums contains the certificate serial numbers that could not be set up for automatic renewal.
ErrorList contains the corresponding error description.
Error text returned:Record not found.
The One or more certificates cannot be set up for automatic renewal. SerialNums contains the certificate serial numbers that could not be set up for automatic renewal. is confusing because i was not trying to do automatic renewal. The Error text returned:Record not found. was correct.