There are times when you are running a job, and you want to do some work as a different userid.
You can configure a userid so it acts as a surrogate – I can submit jobs with your userid, without knowing your password.
You can have a server and have a thread within the server run as different userid by specifying a userid and password, using the pthread_security_applid_np function. You can also have it logon using a certificate, and it looks up the userid from the certificate.
You can extend/restrict this by specifying an RACF APPL which the user must have access to.
RDEFINE APPL YYYY
PERMIT CLASS(APPL) YYYY ID(COLIN) ACCESS(READ)
SETROPTS RACLIST(appl ) REFRESH
My job running with userid IBMUSER specifies a userid COLIN, and COLIN’s password. If applid YYYY is specified, userid COLIN must have read access to the YYYY in CLASS(APPL).
If you use pthread_security_np() is the same as pthread_security_applid_np() and uses the default OMVSAPPL.
My example C program is
Main
int main( int argc, char *argv[])
{
pthread_t thid;
int rc;
void *ret;
if (pthread_create(&thid, NULL, thread, "thread 1") != 0) {
perror("pthread_create() error");
exit(1);
}
rc =pthread_join(thid, &ret);
printf("Pthread join %d\n",rc);
if (rc != 0) {
// perror("pthread_create() error");
// return(3);
}
printf("thread exited with '%s'\n", ret);
return 0 ;
}
#pragma runopts(POSIX(ON))
/*Include standard libraries */
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <stdarg.h>
#include <errno.h>
#define _OPEN_SYS 1
#include <pthread.h>
void *thread(void *arg) {
char *ret = "";
int rc;
printf("thread() entered with argument '%s'\n", arg);
rc = pthread_security_applid_np(__CREATE_SECURITY_ENV,
__USERID_IDENTITY,
5,
"COLIN",
"PASSW0RD",
0,"AAAA");
perror("perror");
printf("colin rc = %d errno %d\n",rc,errno);
if (rc == 0)
{
FILE * f2 ;
f2 = fopen("DD:TEST","r ") ;
printf("DD:TEST %d\n",f2);
}
pthread_exit(ret);
}
int main( int argc, char *argv[])
{
pthread_t thid;
int rc;
void *ret;
if (pthread_create(&thid, NULL, thread, "thread 1") != 0) {
perror("pthread_create() error");
exit(1);
}
rc =pthread_join(thid, &ret);
printf("Pthread join %d\n",rc);
if (rc != 0) {
perror("pthread_create() error");
return(3);
}
printf("thread exited with '%s'\n", ret);
return 0 ;
}
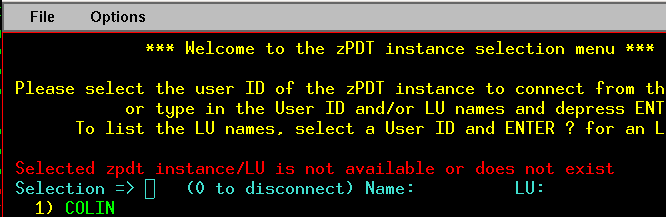
When the above program ran it gave me
ICH408I USER(COLIN ) GROUP(SYS1 ) NAME(COLIN PAICE )
IBMUSER.TRY.PEM CL(DATASET ) VOL(C4USR1)
INSUFFICIENT ACCESS AUTHORITY
ACCESS INTENT(READ ) ACCESS ALLOWED(NONE )
which shows that the userid COLIN was used.
EDC5167I Access to the UNIX System Services version of the C RTL is denied. (errno2=0xC10F0001 C10F0001) .
You cannot use the pthread_security… functions in the main thread. You have to attach a subtask using pthread_create().
EDC5143I No such process. (errno2=0x0BE80000 0BE80000)
Invalid userid specified.
EDC5111I Permission denied. (errno2=0x0BE80000 0BE80000)
Invalid password.
EDC5163I SAF/RACF extract error. (errno2=0x0BE8081C 0BE8081C)
Revoked userid.
EDC5168I Password has expired. (errno2=0x0BE80000 0BE80000)
Obvious.
EDC5163I SAF/RACF extract error. (errno2=0x0BE80820 0BE80820)
No OMVS segment, or the new user does not have access to the specified applid class.
rc = pthread_security_np() defaults to pthread_security_applid_np() with an applid of OMVSAPPL
ICH70004I
ATTEMPTED 'READ' ACCESS OF USER(ADCDE) GROUP(TEST) NAME(ADCDE) ENTITY 'OMVSAPPL' IN CLASS 'APPL'
EDC5139I Operation not permitted. (errno2=0x0BE802AF 0BE802AF)
ICH420I PROGRAM CERT FROM LIBRARY COLIN.LOAD CAUSED THE ENVIRONMENT TO
BECOME UNCONTROLLED.
BPXP014I ENVIRONMENT MUST BE CONTROLLED FOR SERVER (BPX.SERVER)
PROCESSING.
Needed
RALTER PROGRAM CERT ADDMEM('COLIN.LOAD'//NOPADCHK)
SETROPTS WHEN(PROGRAM) REFRESH