My two day project to deploy IP V6 dynamic routing, turned into an eight week project before I got it to work.
I am documenting a lot of what I learned – today’s experience is understanding what radvd is and what the configuration options mean. I found a lot of documentation – most of which either assumed you know a lot, or only provided an incomplete description.
High level view of what radvd provides
There are several ways of providing configuration to TCPIP. One way is using radvd (on Linux).
In a configuration file you give
- An interface name
- Which IP addresses (and address ranges) are available at the remote end of the connection.
- Which IP addresses (and address ranges) are available at the local end of the connection
From the information about the local end, the remote end can build its routing tables.
Background IP routing
With IP you can have
- static routing, where you explicitly give the routes to a destination – such as to get to a.b.c.d – go via xyz interface. You have to do a lot of administration defining the addresses of each end of an interface (think Ethernet cable)
- dynamic routing, and neighbourhood discovery, where the system automatically finds the neighbours and there is less work for an administrator to do.
With IPv6 you have
- global addresses with IP addresses like 2001:db8:1:16…..
- link-local addresses. These are specific to an interface. An Ethernet connection can have many terminals hanging off ‘the bus’. The link-local address is only used within the connection. A different Ethernet cable can use the same address. There is no problem as the addresses are only used with the cable.
- Neighbour Discovery. Rather than specify every thing as you do with static routing, IP V6 supports Neighbour Discovery, where each node can tell connected nodes, what routes and IP addresses it knows about. This is documented in the specification. This supports
- Router Advertisement (RA), (“Hello, I’m a router, I know about the following addresses and routes”),
- Router Solicitation (RS), (“Hello, I’ve just started up, are there any routers out there?”),
- Neighbour Solicitation(NS) (“Does anyone have this IP address?”), and
- Neighbour Advertisement (Usually in response to a Neighbour Solicitation, “I have this address”).
What is radvd?
The radvd program is a Router Advertisment Daemon (RADvd) which provides fakes router information – but is not a router.
You specify a configuration file. The syntax is defined here.
You can specify that this interface provides a “default” route. See here.
Example definition
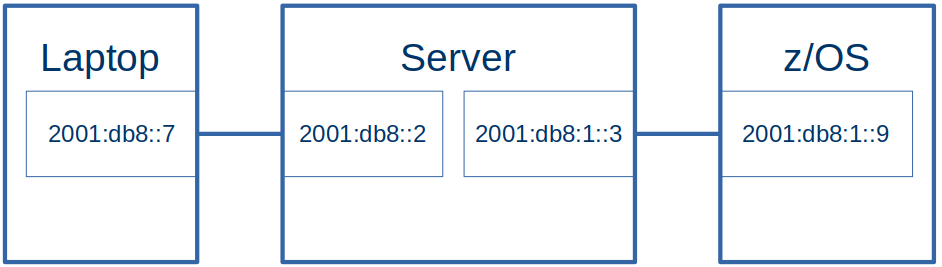
I have a Linux Server, and a laptop running Linux connected by an Ethernet cable.
For the server, the radvd.conf file has
# define the ethernet connection
interface eno1
{
AdvSendAdvert on;
MaxRtrAdvInterval 60;
MinDelayBetweenRAs 60;
prefix 2001:ccc::/64
{
# AdvOnLink on;
# AdvAutonomous on;
AdvRouterAddr on;
};
# route 2001:ff99::/64
# {
# # AdvRoutePreference medium;
# # 3600 = 1 hour
# AdvRouteLifetime 3600;
#
# };
};
The key information is
Comments
Data following #
The name of the interface
interface eno1{….};
prefix statement
prefix 2001:ccc::/64{…}
2001:ccc::/64 is the ipv6 address range or, to say it another way, ipv6 addresses with the left 64 bits beginning with 2001:0ccc:0000:0000. In IP V6 this is known as the prefix.
Basically this prefix statement means “this interface is a route to the specified prefix”.
This creates some addresses on the server for the connection.
eno1 inet6 2001:ccc::e02a:943b:3642:1d73/64 scope global temporary dynamic...
eno1 inet6 2001:ccc::dbf:5c90:61a6:20ae/64 scope global dynamic mngtmpaddr...
eno1 inet6 2001:ccc::c48b:e8f1:495c:5b52/64 scope global temporary dynamic ...
eno1 inet6 2001:ccc::2d8:61ff:fee9:312a/64 scope global dynamic mngtmpaddr ...
create routes
The prefix statement creates a route on the server to get to the laptop
2001:ccc::/64 dev eno1 proto ra metric 100 pref medium
2001:ccc::/64 dev eno1 proto kernel metric 256 ...
This says that on the server, if there is a request for an address in the range 2001:ccc::/64 send it via device eno1.
route 2001:ff99::/64 statement.
If present this passes information to the remote end of the connection, see below. It says “I (the server) know how to route to 2001:ff99::/64”.
It the routing address does not show up in any ip -6 commands on the server.
I could see the Route Information data flowing across the network within a Router Advertisment packet. But I could not see it being used at the remote end.
I think the best thing to do is ignore the route statement.
Polling
The radvd code periodically sends information along the connection to the other end, at an interval you specify. See radvdump below on how to display it.
At the other end of the connection…
At the remote (laptop) end of the connection, using WiresShark to display the data received, shows a Router Advertisement with
Internet Protocol Version 6, Src: fe80::a2f0:9936:ddfd:95fa, Dst: ff02::1
Internet Control Message Protocol v6
Type: Router Advertisement (134)
...
ICMPv6 Option (Prefix information : 2001:ccc::/64)
ICMPv6 Option (Route Information : Medium 2001:ff99::/64)
ICMPv6 Option (Source link-layer address : 00:d8:61:e9:31:2a)
Where
- fe80::a2f0:9936:ddfd:95fa is the link-local address on the server machine
- ff02::1 the multicast address “All nodes” on a link (link-local scope)”
- Prefix information : 2001:ccc::7/64 the prefix of the IP address 2001:ccc:0:0…
- Route Information : Medium 2001:ff99::/64 This is from the “route” in the radvd configuration file on the Linux Server. It tells the laptop that this connection knows about routing to 2001:ccc::/64 .
From the route information it dynamically creates a route on the laptop to the server.
2001:ff99::/64 via fe80::a2f0:9936:ddfd:95fa dev enp0s31f6 proto ra metric 100 ...
This creates a route to 2001:ff99::/64 via the IP address fe80::….95fa, from the laptop end of the Ethernet connection with name enp0s31f6 to where-ever the connection goes to (in this example it goes to my server).
If I ping 2001:ffcc::9 from the laptop, it will use this route on its way to the z/OS server.
Connection to z/OS
Within the radvd.conf file is the definition to get to z/OS. This interface looks like an Ethernet (the ip -6 link command gives link/ether). This is for a different radvd configuration file to the earlier example.
interface tap1
{
AdvSendAdvert on;
MaxRtrAdvInterval 60;
MinDelayBetweenRAs 60;
AdvManagedFlag on;
AdvOtherConfigFlag on;
prefix 2001:db8:1::/64
{
AdvOnLink on;
AdvAutonomous on;
AdvRouterAddr on;
};
prefix 2001:db8:1::99/128
{
AdvOnLink on;
AdvAutonomous on;
AdvRouterAddr on;
};
route 2001:db8::/64
{
AdvRoutePreference medium;
AdvRouteLifetime 3100;
};
};
This says there are IP addresses in the range 2001:db8:1::/64 via this connection. z/OS reads the Router Advertisement and creates a route for them. TSO Netstat route gives
DestIP: 2001:db8:1::/64
Gw: ::
Intf: IFPORTCP6 Refcnt: 0000000000
Flgs: UD MTU: 9000
The explicit IP address, with the 128 to specify use the whole value, rather than just the prefix,
prefix 2001:db8:1::99/128
{
AdvOnLink on;
AdvAutonomous on;
AdvRouterAddr on;
};
creates a route in z/OS; from TSO NETSTAT ROUTE
DestIP: 2001:db8:1::99/128
Gw: ::
Intf: IFPORTCP6 Refcnt: 0000000000
Flgs: UHD MTU: 9000
In UHD, the U says the interface is Up, the H says this is for a host (a specific end point), and the D says this is dynamically created.
If you try to ping 2001:db8:1::99 from the server, a Neighbour Solicitation request is sent from the server to z/OS, asking “do you have 2001:db8:1:99?”. My z/OS did not have that defined and so did not respond.
When I defined this address on z/OS TCPIP using the obeyfile
INTERFACE IFPORTCP6 DELETE
INTERFACE IFPORTCP6
DEFINE IPAQENET6
CHPIDTYPE OSD
PORTNAME PORTCP
INTFID 7:7:7:7
INTERFACE IFPORTCP6
ADDADDR 2001:DB8:1::9
INTERFACE IFPORTCP6
ADDADDR 2001:DB8:9::9
INTERFACE IFPORTCP6
ADDADDR 2001:DB8:1::99
(And used
- v tcpip,,sto,ifportcp6
- v tcpip,,obeyfile,USER.Z24C.TCPPARMS(IFACE61)
- v tcpip,,sta,ifportcp6
to activate it)
After this, the ping was successful because there was a neighbour solicitation for 2001:db8:1::99, and z/OS replied with Neighbour Advertisement of 2001:db8:1::9 saying I have it.
Create a default route
If you specify AdvDefaultLifetime 0 on the interface, this indicates that the router is not a default router and should not appear on the default router list in the Router Advertiser broadcasts. If the value is non zero, the recipient, can use this connection as a default route, for example there is no existing default route. A statically defined default will be used in preference to a dynamically defined one.
Use radvdump to display what it sent in the RA
You can use sudo radvdump to display what is being sent in the Router Advertiser message broadcast over multicast. It looks just like the radvd.conf file, but with all of the values filled in, so you can see the defaults.